Your SOC 2 Type II auditor asks for evidence that employees acknowledged the information security policy. You produce a spreadsheet: names, dates, "Acknowledged" checkboxes. The auditor accepts it. The audit passes.
But here is the question nobody in that room asked: did anyone read it?
SOC 2 Type II audits require more than showing a policy exists. The policy must be current, assigned, acknowledged, and backed by evidence. Most SaaS companies satisfy this requirement with an LMS completion record or a signed acknowledgement form. The auditor checks the box. But the checkbox does not answer whether an engineer who acknowledged the incident response plan could execute it under pressure. It does not tell you whether the new hire who signed the acceptable use policy on day one read past the first paragraph.
For companies that treat SOC 2 as a trust signal for customers - rather than a compliance exercise to survive - the gap between "acknowledged" and "read" matters.
What SOC 2 Trust Services Criteria Require
SOC 2 is built on Trust Services Criteria (TSC), organized into five categories: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Security is mandatory for every SOC 2 report. The others are optional but commonly included.
Two criteria directly govern policy communication and employee awareness:
CC2.2 - Internal Communication. The entity internally communicates information, including objectives and responsibilities for internal control, necessary to support the functioning of internal control. In practice, this means publishing and distributing security policies to all employees through multiple channels - policy repository, employee handbook, onboarding training, and regular security awareness communications - with evidence of distribution such as acknowledgement receipts.
CC1.4 - Accountability. The entity demonstrates a commitment to attract, develop, and retain competent individuals in alignment with objectives. This includes establishing a disciplinary process for policy violations and documenting consequences for security incidents caused by negligence.
The connection between these two criteria is direct: you cannot hold someone accountable for violating a policy they never read. CC1.4 depends on CC2.2. If your evidence for CC2.2 is weak, your CC1.4 controls are undermined.
SOC 2 Type I audits evaluate the design of controls at a point in time. Type II audits evaluate the operating effectiveness of controls over a period (typically 12 months). For Type II, auditors need evidence that policy acknowledgement happened consistently throughout the period - not just that the process exists on paper.
What Auditors Request During a SOC 2 Examination
When a SOC 2 auditor examines your policy communication controls, they request specific evidence. Understanding what they ask for reveals where most companies have gaps:
The policy itself. Current version, with revision history and approval signatures. All policies must be formally documented and integrated into daily operations.
Distribution records. How was the policy delivered to employees? Email, intranet posting, LMS assignment? The auditor verifies the delivery mechanism.
Acknowledgement evidence. A roster or report showing which personnel acknowledged the policy, when they acknowledged it, and whether new hires completed acknowledgement within the required onboarding window.
Training completion records. All employees should have completed security awareness training within the past 12 months, tracked in a learning management system with dates and - where applicable - scores.
Evidence of periodic updates. When policies change, affected employees must be re-acknowledged within 30 days. The auditor checks whether version-specific acknowledgements exist.
Most SaaS companies can produce all five items. The acknowledgement evidence is typically a report from an LMS or HR system showing completion dates. This satisfies the auditor's procedural check.
But it tells the auditor nothing about engagement. And increasingly, sophisticated auditors - and the enterprise customers reading your SOC 2 report - are asking harder questions.
Where Checkbox Acknowledgement Falls Short
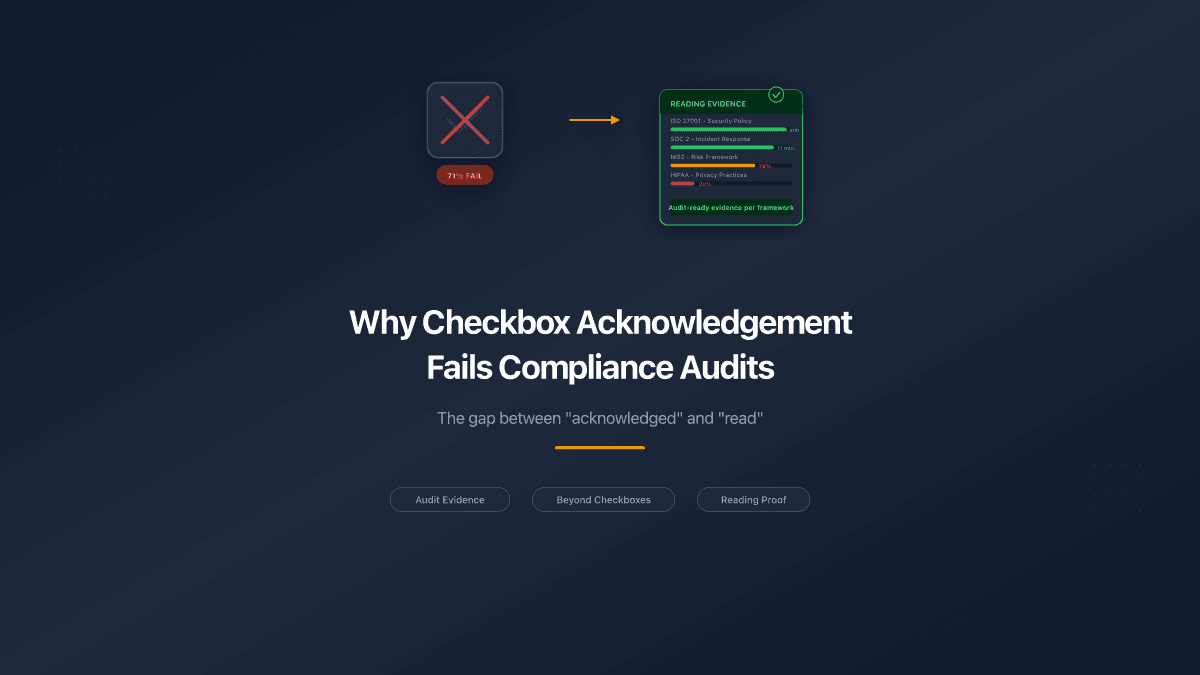
The standard SOC 2 evidence package - policy document, LMS completion record, signed acknowledgement form - has three structural weaknesses:
It proves delivery, not reading. An LMS marks a module as "complete" when the employee reaches the end. It does not distinguish between someone who read every screen and someone who clicked "Next" repeatedly for 45 seconds. A signed acknowledgement form proves the employee saw a document and agreed to its terms. It does not prove they opened the PDF.
It provides no engagement metrics. When your enterprise customer's security team reviews your SOC 2 report and asks "how do you ensure your engineers understand the incident response plan?", the answer is a completion date. Not a reading time. Not a completion percentage. Not evidence of which sections received attention.
It creates a false sense of coverage. The dashboard shows 100% completion. Every employee acknowledged every policy. In reality, a portion clicked through without reading. The compliance team has no way to identify who engaged and who did not - until an incident reveals the gap.
These weaknesses do not cause SOC 2 audit failures today. Most auditors accept checkbox acknowledgement as sufficient evidence for CC2.2. But the gap between the evidence standard and the security standard is real - and it surfaces when incidents occur.
What Stronger Evidence Looks Like
Companies that want their SOC 2 controls to reflect actual security posture - not just procedural compliance - need evidence that goes beyond checkboxes:
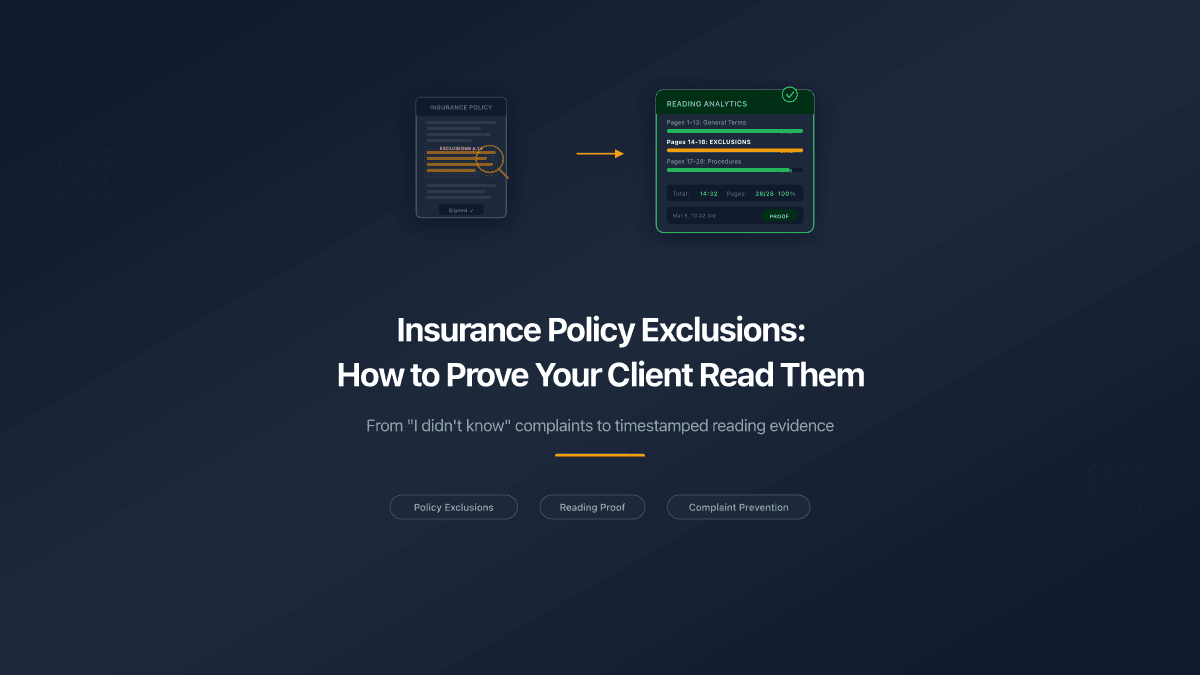
Page-level engagement data. When an engineer is assigned the incident response policy, page-level analytics show whether they viewed every section. A 20-page policy "completed" in 30 seconds is not engagement. Consistent reading time across pages over several minutes is.
Role-specific distribution records. SOC 2 requires role-specific training for personnel in security-relevant positions. Your evidence should show that the DevOps team received the change management procedure, the support team received the data handling policy, and the engineering team received the secure development lifecycle document - not that everyone got the same PDF.
Version-controlled acknowledgement. When the access control policy is updated after a quarterly review, the acknowledgement trail shows who completed the new version versus the old one. The auditor sees version-specific evidence, not a generic "acknowledged" flag.
Onboarding window compliance. SOC 2 auditors check whether new hires completed security training within the required onboarding period. Reading analytics with timestamps establish exactly when the new hire engaged with each policy - not just when they clicked "complete."
Tab visibility and anti-gaming. The reading timer pauses when the employee switches to Slack, email, or another browser tab. This ensures the engagement data reflects actual reading, not a document left open in a background tab.
| Evidence Type | Checkbox Approach | Reading Analytics |
|---|---|---|
| CC2.2 - Distribution | "Policy emailed on Jan 15" | "Policy viewed on Jan 15, all 12 pages, 8 min" |
| CC2.2 - Acknowledgement | "Acknowledged on Jan 16" | "Read pages 1-12, returned to Section 4 (incident reporting) on Jan 17" |
| CC1.4 - Competence | "Training completed" | "Incident response plan: 14 min reading, 100% completion" |
| New hire onboarding | "Completed within 7 days" | "Day 2: read acceptable use (6 min). Day 3: read data handling (9 min). Day 5: read incident response (11 min)." |
| Policy update | "Re-acknowledged on Mar 1" | "Read updated access control v3.1 on Mar 1, focused on Section 7 (new MFA requirements)" |
The Policies That Matter Most
SaaS companies maintain anywhere from 10 to 25 security policies for SOC 2. Not all carry equal weight in practice. The policies where reading verification has the highest impact:
Incident response plan. When a breach occurs at 2 AM, the on-call engineer needs to know the escalation path, the communication protocol, and the containment steps. This is not a document people can reference calmly during an incident. They need to have read it beforehand.
Access control policy. Who can access what, under which conditions, with which approvals. Every access-related SOC 2 finding traces back to whether the person requesting or granting access understood the policy.
Acceptable use policy. The boundary between personal and professional use of company systems. Violations often stem from ignorance, not malice - an employee who never read the policy on personal device management introduces risk unknowingly.
Change management procedure. How code moves from development to production. A developer who bypasses the change approval process because they never read the procedure creates exactly the kind of finding that appears in SOC 2 reports.
Data classification and handling. Which data is confidential, how it must be stored, who can access it. An engineer who pushes customer data to a staging environment because they did not read the data handling policy creates a reportable incident.
SOC 2 auditors pay specific attention to changes during the audit period. If a policy was updated mid-year, they check whether all affected employees re-acknowledged the new version. Version-specific reading data is stronger evidence than a generic re-acknowledgement prompt.
How This Works for SaaS Security Teams
The workflow integrates with whatever policy management approach you already use:
- Upload the security policy to a document sharing platform with reading analytics
- Generate tracked links per team, per role, or per individual
- Distribute through existing channels - Slack, email, the company wiki, or your GRC platform
- Employees click the link and read in a browser-based viewer - no app download needed
- The analytics engine records viewing sessions: pages viewed, time per page, completion, timestamps
- The security team exports a report showing per-employee engagement data for the audit period
For SOC 2 Type II audits, the export covers the full observation period. The auditor sees not just who acknowledged which policy, but when they read it, how thoroughly, and whether they engaged with updated versions.
The employee experience is simple: click a link, read a document. The security team gets evidence that differentiates genuine engagement from procedural compliance.
SOC 2 as a Trust Signal
SOC 2 started as an assurance framework for service organizations. It has become a sales requirement. Enterprise buyers request SOC 2 Type II reports before signing contracts. Security teams at prospective customers review the report's control descriptions and test results.
When a prospective customer's CISO reads your SOC 2 report and sees "security policies are distributed to all employees and acknowledged annually," they understand the minimum standard is met. When they see evidence that your team's reading engagement is tracked at the page level - with anti-gaming protections and role-specific distribution - they see a security program that goes beyond compliance theatre.
The difference between passing the audit and earning trust is the quality of evidence behind each control. Checkbox acknowledgement passes the audit. Reading analytics earn the trust.
PaperLink tracks page-by-page viewing analytics for shared documents - including time per page, completion percentage, and tab visibility detection. SaaS security teams use it to generate SOC 2 evidence showing genuine policy reading engagement across all employee roles. Try it free.