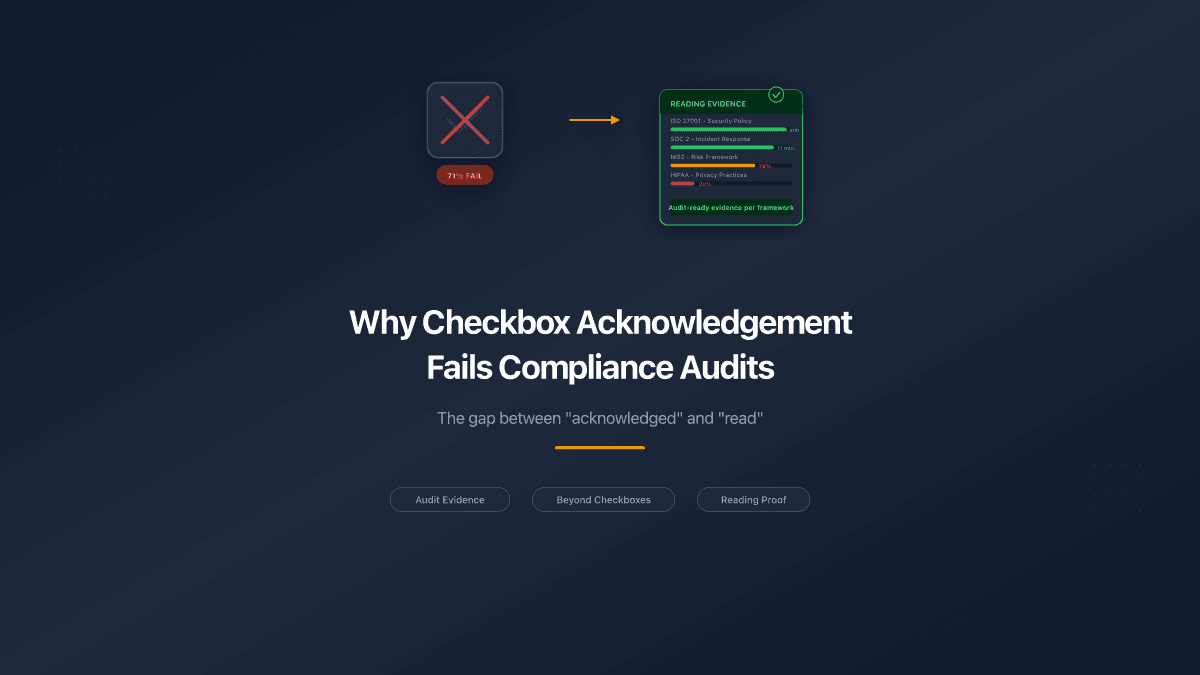
Your employees didn't read that security policy. They clicked "I acknowledge" and moved on with their day.
You know it. They know it. And when an auditor or a lawyer asks for proof of reading, that checkbox is the only thing standing between your company and a compliance gap.
This is the state of policy acknowledgement in most organizations: a legal fiction that satisfies nobody. HR distributes a 30-page Information Security Policy through PeopleForce, Zoho, or BambooHR. The system records "acknowledged" next to each name. But acknowledged and read are two different things - and the difference matters more than most companies realize.
Why "Acknowledged" Doesn't Mean "Read"
Every HR system handles policy distribution the same way. Upload the document, assign it to employees, collect a checkbox or e-signature. Done.
The problem: none of these systems verify that the employee opened the document, let alone read it. A checkbox acknowledgement confirms receipt - not comprehension, not even viewing. It's the compliance equivalent of signing for a package you never opened.
This matters for three reasons:
Legal exposure. In employment disputes, companies rely on signed acknowledgements as proof the employee knew the rules. But courts increasingly question whether a checkbox proves awareness. Without documented proof of actual communication, your employee handbook provides limited legal protection.
Audit failures. ISO 27001 auditors don't just check that policies exist - they verify that policies are "accessible to those who need it" and that employees received "appropriate awareness education and training" (ISO 27001, Annex A.7.2.2). A checkbox doesn't demonstrate awareness. SOC 2 audits require the same: signed acknowledgements with evidence that policies are maintained and accessible.
Security incidents. When a breach happens, the first question is: "Did the employee know the policy?" If your only evidence is a checkbox from six months ago, you carry the liability. Security teams write detailed Acceptable Use Policies, Incident Response Plans, and Data Classification guides - then have zero visibility into whether anyone reads them.
The Checkbox Problem Is Getting Worse
New regulations are raising the bar from "distribute policies" to "prove people understand them."
NIS2 Directive - mandatory across the EU from 2026 - explicitly requires that organizations demonstrate policies function through people's behavior, not just their existence. Article 20 mandates cybersecurity training for management and employees across 160,000+ companies in 18 sectors. A checkbox won't satisfy this.
DORA - the EU's Digital Operational Resilience Act for financial institutions - requires all employees and senior management to complete ICT security awareness training appropriate to their roles. Regulators expect documented proof of completion, not acknowledgement forms.
GDPR requires companies to demonstrate compliance through auditable records that employees handling personal data understand data protection policies.
HIPAA mandates regular training on accuracy, documentation, and knowledge of organizational policies for healthcare workers.
The pattern is clear: regulators worldwide are moving from "did you distribute it?" to "can you prove they engaged with it?" Checkboxes answer the first question. They fail the second.
What Real Proof of Reading Looks Like
Genuine reading verification tracks what happens after the employee opens the document - not just whether they clicked a button.
Page-level time tracking. How long did the employee spend on each page? A 20-page security policy read in 30 seconds is not reading. A consistent 45-90 seconds per page over 15 minutes is. This is the difference between proof and theatre.
Completion percentage. Did they view every page, or did they scroll to the bottom and close? Opening a document and jumping to the signature page is the digital equivalent of flipping to the last chapter of a textbook.
Tab visibility detection. If the employee opens the document and switches to another browser tab, the timer stops. Reading time is only counted when the document is actively visible on screen. This prevents the "open it and go get coffee" workaround.
Return visit tracking. Real reading often happens across multiple sessions. Someone opens the policy on Monday for three minutes, returns Wednesday to finish. Both sessions are recorded. The compliance officer sees the complete picture.
Reading speed analysis. A dashboard that highlights unrealistic patterns - documents "completed" in impossibly short times - gives HR a targeted follow-up list instead of blind trust.
The output: instead of "342 out of 400 employees clicked acknowledge," compliance teams can report "85% of employees completed the Information Security Policy, with an average reading time of 14 minutes across 12 pages. 47 employees have not completed reading. 12 showed reading patterns below the expected threshold."
That's audit-ready evidence. That's what NIS2, SOC 2, and ISO 27001 auditors want to see.
How This Works in Practice
The workflow doesn't require employees to learn a new tool or change their habits:
- HR uploads the policy document (PDF, Word, any format) to a document sharing platform with built-in analytics
- The platform generates a unique tracked link for each employee - or a single link that identifies viewers by email
- HR distributes the link through the existing HR system (PeopleForce, Zoho People, BambooHR, or email)
- Employees click the link and read in a secure browser-based viewer - no downloads, no plugins
- The analytics engine tracks every viewing session: pages viewed, time per page, completion, return visits
- The platform pushes reading status back to the HR system via API - updating the employee's profile automatically
The employee experience is simple: click a link, read a document. The compliance team gets page-level proof of engagement without adding steps to the process.
Who Needs This
This isn't a niche problem. Every regulated industry requires documented proof that employees understand company policies:
| Industry | Why reading proof matters | Key regulations |
|---|---|---|
| Finance & Banking | AML policies, fraud prevention, data handling | DORA, SOX, Dodd-Frank |
| Healthcare | Patient data protection, clinical procedures | HIPAA, GDPR |
| Technology & SaaS | Security policies, data processing agreements | SOC 2, ISO 27001 |
| Critical Infrastructure | Cybersecurity, operational resilience | NIS2 |
| Legal Services | Client confidentiality, conflicts of interest | Bar regulations |
| Manufacturing | Safety procedures, quality standards | ISO 9001, OSHA |
Security teams have an especially urgent need. Every policy they write - Acceptable Use, Incident Response, Data Classification, Access Control - depends on employees knowing the content. When a breach investigation starts with "did the employee know the rules?", the answer can't be "they clicked a checkbox six months ago."
NIS2 compliance language is explicit: "It is no longer enough to have policies - organizations must demonstrate that they function through people's behavior." This applies to 160,000+ companies across the EU starting in 2026.
Beyond Checkboxes: What to Look For
If you're evaluating tools for policy reading verification, here's what separates genuine solutions from checkbox upgrades:
Page-level analytics, not document-level. "Opened the document" is not enough. You need time-per-page data that shows actual reading behavior.
Passive tracking, not quizzes. Quizzes test memory, not reading. They add friction and resentment. Reading analytics work silently in the background.
HR system integration. Reading status should flow directly into the employee's HR profile - not live in a separate dashboard that nobody checks.
Anti-gaming protections. Tab visibility detection, reading speed flags, scroll depth tracking. Without these, employees will find workarounds within a week.
Audit-ready exports. One-click PDF or CSV that shows: who read what, when, for how long, completion percentage. This is what you hand to the auditor.
Version-aware redistribution. When a policy is updated, all affected employees should be automatically reassigned. The system tracks acknowledgement per version, not per document.
The Compliance Gap Is a Business Risk
The real cost of checkbox acknowledgement isn't the tool - it's the gap between what you think happened and what actually happened.
When 400 employees "acknowledge" a security policy and 50 of them never opened it, you have 50 people making decisions without knowing the rules. If one of them mishandles data, shares credentials, or ignores an incident response procedure, your checkbox won't protect you.
Regulations are catching up to this reality. NIS2, DORA, SOC 2, and ISO 27001 are all moving toward evidence-based compliance - proof that policies are read, understood, and followed. The companies that adopt reading verification now will pass audits faster, reduce legal exposure, and - most importantly - have employees who actually know the policies that govern their work.
The checkbox had its era. It's time for proof.
PaperLink tracks page-by-page viewing analytics for shared documents - including time per page, completion percentage, and tab visibility detection. Combined with direct HR system integration, it turns policy distribution into verifiable compliance. Try it free.